What is it about?
This work gives a AKE security, aiming to combine the CK model and eCK model, as well as to specify the adversarial capabilities in the security model.
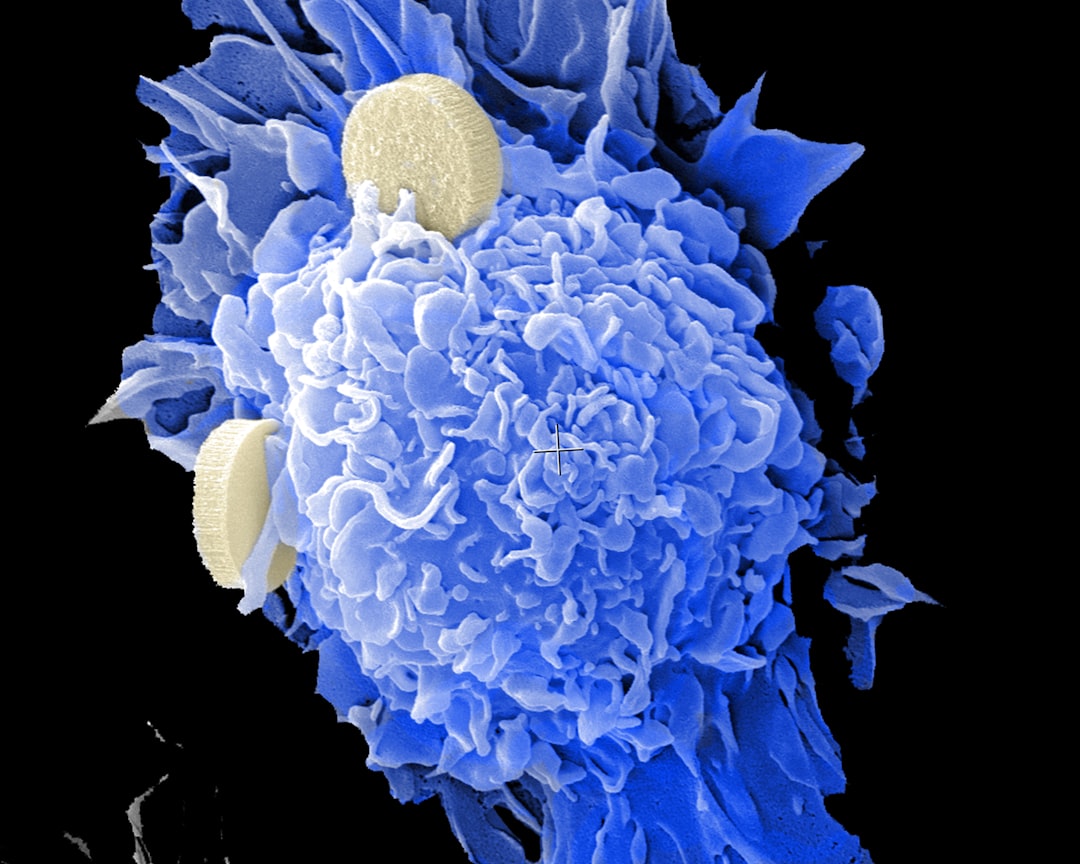
Featured Image
Why is it important?
The model describe the (strong) security requirement of an AKE protocol without ambiguity.
Perspectives
This work packs CK and eCK into a unified security model. The security notions are stronger and the adversarial capabilities have no ambiguity.
Dr Libin Wang
South China Normal University
Read the Original
This page is a summary of: Unified security model of authenticated key exchange with specific adversarial capabilities, IET Information Security, January 2016, the Institution of Engineering and Technology (the IET),
DOI: 10.1049/iet-ifs.2014.0234.
You can read the full text:
Resources
Contributors
The following have contributed to this page